Anycasting
Please create the "Talk page". Just click this Talk page link and save the page.
Anycasting is an Internet Protocol routing technique in which the same IP address may exist at several points in the network, with the caveat that each instance of the address must provide exactly the same services. The technique is useful for load balancing, fault tolerance, and security against a Denial of service|DoS attack. A typical application is a heavily-used database like DNS, where the same data can be provided from any number of identical servers. Applications are not limited to "read-only" however. See the Sinkhole|sinkholes operational example below.
Traditionally, an IP address needed to be unique. This would be absolutely true in a single network with no segmentation. The Internet, however, is a collection of networks linked by routers. When the same address is claimed by servers on different networks, an upstream router simply assumes it is the same server as seen via different routes. It picks the shortest path for its routing table, and ignores the rest. A router supporting anycast keeps these routes available as alternatives. Alternative routes may be selected randomly, in a cyclic pattern, or depending on external factors, such as the current load reported by each server.
While the term anycast came into prominence with IPv6 work,[1] it can be quite useful with IPv4. IPv4 has no infrastructure explicitly for anycast while IPv6 does, but the technique can be applied in both areas, with different address structures. Miller discusses "shared anycast",[2] which is different from the IPv6 specific work in RFC 4291, which superseded the RFC 3513 mentioned in the Miller paper.
The IPv6 architecture describes it as:
Anycast: An identifier for a set of interfaces (typically belonging to different nodes). A packet sent to an anycast address is delivered to one of the interfaces identified by that address (the "nearest" one, according to the routing protocols' measure of distance).[1]
Contrast to multicast
Anycasting is similar to Multicasting. In multicasting, a source S sends to a group G of recipients. Broadcasting is a special case where G contains all possible recipients. It is assumed that G has more than one member.
An anycast source S sends a data packet to a destination address D, which S believes to be a single machine. In reality, there are multiple instances of D, any one of which can receive the packet addressed to D.
Load balancing case
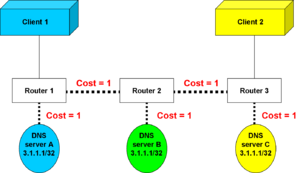
In Figure 1, there are two clients and three servers, all with the same IP address 3.1.1.1. It makes no difference to either client which server satisfies its request.
The traditional routing algorithm adds up the costs of links along the available routes to a destination and always picks the lowest cost route. From client 1, server A is closest (cost=1) and server 3 is furthest (cost=3). Therefore, client 1 always connects to server A, and client 2 always connects to server C.
An anycast router can balance the load among all routes, rapidly switching from one to another. A packet from Client 1 can be routed just as easily to Server C as to Server A.[3]
Fault tolerance case
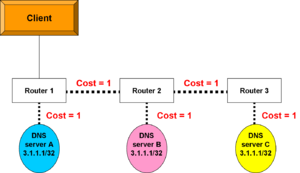
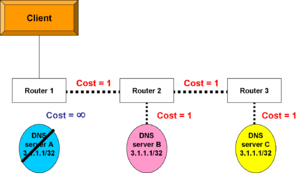
Now, simplify the scenario to have but one client (Figure 2). As long as server A is up, router 1 will see a cost of 1 to reach server A. The routing process was aware of other routes to 3.1.1.1, but there was a cost of 2 to server B and a cost of 3 to server C. Router 1 put only the lowest-cost route into its routing table.
But what if server A fails? The router knows other paths to the same address, so it will install the path that goes through router 2. The client will still receive exactly the same service from exactly the same address.[4] It is a standard rule of router configuration, based on the end-to-end assumption of Internet protocol routing, that IP addresses are unique. Anycasting, however, creates multiple instances of the same address, breaking this rule but in a controlled manner. Some of the constraints on an anycast configuration is that the different instances of the same address must be on separate routers.
Operational examples
Anycast works well for applications that do not require perfect synchronization of changes at the servers and do not need to keep track of sessions or user state. An application requiring the user to log in, for example, might get confused if the session was suddenly switched to a machine on which the user is not logged in.
One common application of anycast is the root servers for the Domain Name System. While the official list has thirteen named servers, there are actually hundreds of geographically distributed machines.
Another application is an active defense against Denial of service|DoS attacks. Instead of just providing more capacity to absorb the attack, or even null-routing it, it is possible to divert the attack to a set of Sinkhole|sinkholes that analyze the traffic, and perhaps even engage with the attacker, trying to elicit traceback information, or even tarpit the attacker's machines.
When an attack is detected, the server under attack would be useless due to overload, so its address is reassigned as an anycast address of a set of sinkholes. For a single-stream attack, the sinkhole nearest the ingress router does the analysis. For a distributed denial of service (DDoS) attack, the entire set of sinkholes may engage the attack flow, multiplying processing power through loose parallelism.
References
- ↑ 1.0 1.1 Hinden, R. & S. Deering. (February 2006), IP Version 6 Addressing Architecture., RFC 4291
- ↑ Miller, Kevin (NANOG 29 – October 2003), Deploying IP Anycast
- ↑ There is some doubt about this statement. See the talk page.
- ↑ Fault tolerance occurs as a result of normal router action, nothing special about anycasting.